Introduction: Why MVP Security Can’t Wait
Many founders assume security becomes relevant only after product-market fit. In reality, MVPs are exposed to real-world threats from the moment they go live.
Today’s MVPs rely on public cloud infrastructure, third-party services, and real user data. This combination makes even early-stage products visible targets. Incidents like the Buffer breach (2013) and the Codecov supply-chain attack (2021) show that attackers often exploit early security gaps, not mature systems.
At the MVP stage, security isn’t about perfection. It’s about avoiding irreversible trust damage while the product is still evolving. This blog explores the often-overlooked aspects of security in MVP development, highlighting the practical decisions founders need to make during the build stage, not after incidents occur.
TL;DR — Key MVP Security Insights
- Secure authentication, APIs, and sensitive data from day one.
- Choose proven tools and services over custom security builds.
- Treat third-party services as part of your attack surface.
- Basic logging and alerts prevent silent failures.
- Security is a shared responsibility, not just an engineering task.
Security Mindset for MVPs
Build-Secure-First, Not Secure-Later
Security debt compounds faster than technical debt. Every insecure shortcut taken early becomes harder and more expensive to fix once users, data, and integrations accumulate.
A secure-first mindset means:
- Defaulting to private, locked-down systems
- Granting access intentionally, not conveniently
- Assuming breach scenarios will happen and designing to limit blast radius
The goal is not to block speed, but to protect learning velocity.
For founders, this simply means: security decisions should be made at design time, not after incidents occur.
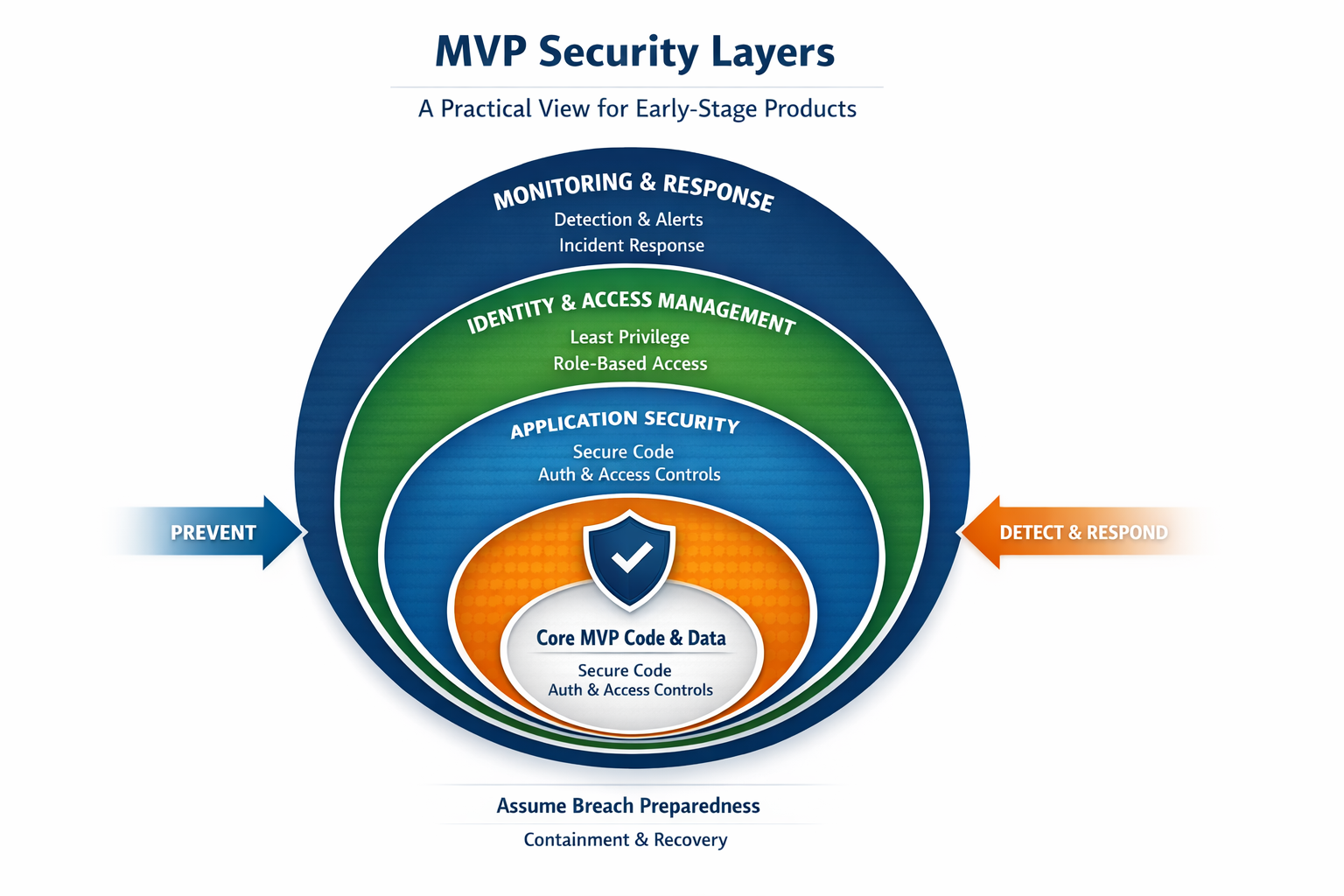
At a practical level, MVP security is not a single feature. It is a layered system where each layer protects a different part of your product.
Security Decision Framework for MVPs
Founders often ask: “What actually needs to be secured right now?”
A simple rule helps: If compromise causes user harm, legal exposure, or revenue loss—it cannot wait.
Examples:
- Authentication → Secure now
- Payment or personal data → Secure now
- Analytics dashboards → Can wait
This framework prevents two common mistakes: over-engineering too early, and under-securing what truly matters.
A Practical MVP Risk Lens
| Product Area / Asset | Risk if Compromised | Business Impact | MVP Action |
|---|
| Authentication | High | Account takeover, data breach | Secure immediately |
| Payments / PII | Critical | Legal penalties, financial loss, loss of trust | Secure immediately |
| Core APIs | High | Data breach, service disruption | Secure immediately |
| Analytics | Low | Minimal impact | Can defer |
| Feature flags/experiments | Low | Minimal impact | Can defer |
Founder insight: If a failure would cause user harm, legal exposure, or investor concern, it does not belong in the “we’ll fix it later” bucket.
Cloud and Infrastructure Security
Shared Responsibility Model
Cloud providers do a solid job of protecting their data centers and underlying infrastructure. But once your product is running in the cloud, the rest is on you. Identity and access controls, exposed APIs, application logic, and customer data all fall under your responsibility.
For founders, this is a critical but often missed aspect of MVP security. Hosting your MVP on a reputable cloud platform does not make it secure by default. In fact, simple misconfigurations in cloud services are one of the most common reasons early-stage products get breached.
Controlled Access Boundaries
Use IAM (Identity and Access Management) to enforce least privilege—each user or service gets only the permissions it absolutely needs.
Avoid shared admin accounts. Use role-based permissions and audit access regularly.
Private Environment Design
Databases, internal services, and admin tools should live inside private networks (VPCs). Only expose what users truly need to access.
Data Protection Fundamentals
Encryption at Rest
Stored data should be encrypted using AES-256—an industry-accepted standard. This ensures that even if backups or disks are leaked, data remains unreadable.
Encryption in Transit
All data transfers should use TLS (HTTPS). Think of TLS as a secure tunnel that prevents eavesdropping while data moves between systems.
Key & Secret Management
Never hardcode secrets in source code. Use secure vaults, rotate keys regularly, and prefer short-lived credentials so leaked keys expire quickly.
Access and Identity Management
Role-Based Access Control (RBAC)
RBAC ensures that people and systems can only do what their role actually requires—nothing more. In the early stages of a product, it’s common for everyone to have broad access just to move fast. But as soon as real user data enters the picture, this becomes a serious risk.
From an MVP security standpoint, RBAC helps limit the blast radius if something goes wrong. A compromised account, a faulty script, or even a simple human error should not have the ability to affect your entire system. By defining clear roles for founders, developers, admins, and automated services, you reduce unnecessary access and make your product safer without slowing down development.
Example:
- Developers deploy code but don’t access production data
- QA tests features but doesn’t modify infrastructure
This dramatically limits damage from compromised accounts.
Authentication Strategy for Early-Stage Products
Authentication failures remain one of the most common root causes of breaches, largely due to weak credential handling and misconfigured access controls.
For founders asking how to build a secure MVP, authentication should be treated as foundational infrastructure—not an area for experimentation. Building custom login systems increases risk without delivering user-facing value.
Best practices for early-stage products include:
- Use managed identity providers (Auth0, Firebase Auth, AWS Cognito, Clerk) that support modern standards like OAuth 2.0 and OpenID Connect.
- Enforce Multi-Factor Authentication (MFA) at least for internal users, admins, and privileged roles. NIST guidance explicitly recommends MFA to reduce account takeover risk.
- Adopt secure password handling by default: strong hashing (bcrypt or Argon2), rate-limited login attempts, and account lockout policies.
- Separate authentication from authorization, ensuring users only access what their role explicitly allows.
Privacy-First MVP Design
Data Minimization
Collect only what’s essential for the MVP to function. Every additional data field increases security and compliance risk.
User Data Control
Give users clear control over their data, including the ability to:
- Download their data
- Delete their account
- Understand how their data is used
These controls build trust early and significantly reduce regulatory friction later.
Secure Development Practices
Code-Level Safeguards
Treat all external input as untrusted. This prevents common attacks like SQL injection and cross-site scripting (XSS). Never assume input is “safe” just because it comes from your own UI; attackers bypass interfaces.
Credential Hygiene
Passwords should never be stored as plain text. Use hashing algorithms like bcrypt or Argon2, which make stolen passwords useless to attackers.
API and Integration Protection
APIs are often the most exposed surface area in an MVP, connecting clients, services, and partners. According to OWASP, authorization flaws and excessive data exposure are among the most exploited API weaknesses.
Key protection measures for MVP APIs include:
- Strong authentication and authorization for every endpoint, not just user-facing ones. Never assume “internal” APIs are safe by default.
- Token-based access (JWTs or OAuth tokens) with short expiration times to reduce the impact of leaked credentials.
- Rate limiting and throttling to prevent abuse, credential stuffing, and unexpected infrastructure cost spikes.
- Input validation and schema enforcement to reduce injection and deserialization risks.
Strong API controls are central to MVP security best practices and reduce systemic risk early.
Third-Party Risk Management
Early-stage products depend heavily on external libraries, SaaS tools, cloud services, and CI/CD pipelines. Each dependency expands the attack surface—often invisibly.
Practical third-party risk controls for MVPs:
- Prefer well-maintained libraries with active communities.
- Maintain a simple inventory of third-party tools and their permissions.
- Monitor dependencies for known vulnerabilities.
- Restrict CI/CD and service account permissions.
Visibility and Monitoring Readiness
Many MVP breaches go unnoticed simply because no meaningful logging exists. Visibility is the foundation of security response.
Even without enterprise tooling, MVPs should log:
- Authentication attempts and failures
- Permission or role changes
- Access to sensitive data and admin features
- Abnormal API error or usage patterns
Basic alerting through email or Slack is sufficient at this stage. Early signals dramatically reduce the time between compromise and response.
Operational Resilience Planning
Backup Readiness
Backups must be automated, encrypted, and tested.
Recovery Assurance
A backup that hasn’t been restored is just an assumption.
Security as a Team Practice
Security outcomes are shaped long before code is written. Product decisions, UX flows, and business priorities all influence risk.
Making security a team practice means:
- Designers avoid dark patterns that encourage unsafe behavior.
- Product managers consider abuse cases alongside user stories.
- Founders prioritize security trade-offs consciously, not reactively.
- Engineers document assumptions and security decisions early.
Lightweight documentation and shared accountability prevent fragile, knowledge-siloed systems—especially as teams scale.
Threat Awareness and Response
Threat modeling is not an enterprise-only exercise. Even simple, structured questioning improves security decisions.
Founders and teams should regularly ask:
- What data would cause the most damage if exposed?
- Which features could be abused at scale?
- What happens if an API key or admin account is compromised?
A basic incident response plan—even a one-page document—should define:
- Who investigates incidents
- How access is revoked
- How users are notified (if needed)
According to SANS Institute guidance, having any response plan is significantly better than improvising during an incident.
Security vs Compliance: What Founders Should Know
Security and compliance are often confused, but they serve different purposes. Security protects your systems and user data from real threats. Compliance proves that certain controls and processes are in place.
Standards like SOC 2 or ISO 27001 are important trust signals, especially when selling to larger customers. But passing an audit doesn’t mean your product is secure. Audits are point-in-time assessments that focus heavily on documentation, while real security depends on how well your systems hold up as your product, team, and infrastructure evolve.
This gap matters even more at the MVP security stage. Early products change fast, and new risks are introduced with every release. A compliant setup can still fail if access is too broad, cloud services are misconfigured, or monitoring is weak. Attackers don’t target your policies; they exploit what’s actually running in production.
The key takeaway for founders is straightforward: build real security first. When your product is designed with clear access controls, sensible defaults, and ongoing monitoring, compliance becomes much easier to achieve later—and far more meaningful when you do.
Conclusion: Secure MVPs Scale Faster
Security is not a feature you “add later”—it’s the foundation on which your MVP earns trust, scales responsibly, and survives real-world threats. Founders who embed security early avoid costly rewrites, reduce breach risk, and build confidence with users, partners, and investors alike. The goal isn’t perfection, but intentional protection: securing what matters most while moving fast and learning faster.
If you’re building an MVP and want to balance speed with real-world security, Splitbit Innovative Solutions helps early-stage teams design, build, and scale products with secure-by-default architectures—without slowing innovation. Whether you’re validating an idea or preparing for scale, partnering early on security can save months of rework and years of risk.